How To Remove Rakuten From Chrome
Threat SummaryRakuten Virus — How Did I Get It?Rakuten Virus — What Does It Do?Remove Rakuten Virus from Your Machine
 What are Rakuten viruses? Is a Rakuten virus unsafe? How to remove a Rakuten virus from your calculator?
What are Rakuten viruses? Is a Rakuten virus unsafe? How to remove a Rakuten virus from your calculator?
Rakuten virus infections can happen through multiple means. They take advantage of the name of the shopping site in guild to promote themselves. The different virus attacks are being operated past different hacking groups and individuals — nosotros have received reports of numerous campaigns that use the Rakuten name in different elements. Most of them are related to malicious scripts that are constitute in redirects and pop-ups, as well as intrusive ads. Reading this commodity will aid you lot protect yourself from bogus Rakuten sites and virus infections.

Threat Summary
| Name | Rakuten Virus |
| Type | Malware |
| Short Description | Virus that takes reward of the legitimate and famous shopping site Rakuten. |
| Symptoms | The symptoms may exist ranging from seeing redirects to having symptom-less Trojan on your calculator. |
| Distribution Method | Bundled downloads. Web pages which may advertise information technology. |
| Detection Tool | See If Your Arrangement Has Been Affected by malware Download Malware Removal Tool |
| User Experience | Join Our Forum to Talk over Rakuten Virus. |

Rakuten Virus — How Did I Become Information technology?
The Rakuten virus can manifest itself in multiple ways depending on the blazon of virus and the hacking commonage behind the ongoing attacks. Equally this is a collection of different types of viruses it is very possible for several infections to be launched at the aforementioned time past different hackers.
One of the most popular infections that are popular with such threats is the coordination of hacker-made fake sites that volition impersonate the official Rakuten site and whatever of its subsections. They are usually hosted on similar sounding domain names and may include stolen or self-signed security certificates. Any interaction with these sites tin lead to further virus infections or certain phishing pages that will manipulate the victims into entering in their Rakuten account credentials or private data.
In a similar way the hackers behind the threat may also send out phishing emails that impersonate the official site and may contain whatever of the post-obit content: advert, links to simulated pages, countersign reset reminders and etc. Without regard to the included contents whatsoever interaction with the emails can lead to further virus infections.
Rakuten virus lawmaking tin can also exist placed inside different types of files including the post-obit examples:
- Malicious Documents — This is the creation of malicious documents that include dangerous macros code. These documents can be of all popular formats: spreadsheets, presentations, databases and text files. When they are opened past the users a prompt volition request them to enable the born scripts. If this is done the virus will be installed.
- Bundle Installers — This is a popular method which is the creation of numerous installers of pop application which are distributed to the target end users. This is washed by taking the original and legitimate data from their official sources and modifying them to include the relevant malware lawmaking. The apps can exist productivity tools, creativity suites, office programs and even computer games.
- Browser Plugins — The plugins, alternatively known as hijackers are unremarkably found on the associated app repositories. They are uploaded with simulated user reviews and developer credentials. The associated descriptions will include promises of new features addition and performance optimizations.
All of these files can be uploaded to file-sharing networks such as BitTorrent where both legitimate and pirate fies can be found. The infections can besides be acquired by other malicious threats that include the payload delivery code.

Rakuten Virus — What Does It Practise?
As soon as i of the variants of the Rakuten virus has infected a given reckoner the built-in engine will outset the congenital-in sequence of malicious deportment based on the local conditions or the hackers instructions. Depending on the form and type of virus dissimilar effects can happen.
All web-based versions (sites, emails and hijackers) are usually associated with the web browser action. Their scripts will hijack the contained within information and transmit it to the operators. This includes the following: cookies, bookmarks, settings, history and fifty-fifty stored account credentials. What'due south unsafe nearly having admission to the browsers is that information technology provides a very easy way for the hackers to spy on the victims.
1 of the most common consequences of web-based attacks is the manipulation of the browsers into opening upwards a hacker-controlled page. his volition allow them to trick the users into interacting with malicious content that volition exist pushed to them in an intrusive mode. The malicious sites can lead to the following behavior:
- Malware Redirects — When the pages are opened the users can be automatically redirected to another site via a script.
- Users Tracking — Using tracking cookies and other technologies the victims tin can be tracked across the sites in real-fourth dimension. All of their activities will be transmitted to the hackers in real-time.
- Cryptocurrency Miners Installation — Many of the malicious spider web sites can pb to a miner infection. These are small-sized scripts that will download a sequence of circuitous mathematical tasks which will identify a heavy toll on the operation of the machines: the CPU, memory, difficult deejay infinite and etc. For every reported successful task the hackers volition exist awarded with digital cryptocurrency.
- Adware Presentation — These pages tin present intrusive ads in all pop forms: banners, pop-ups, text links and etc. For every display or interaction with them the hackers will receive payment by the advertisers.
All of these pages can be function of a worldwide network of connected sites which ways that there is a high probability that the collected information may be part of a worldwide database of victim information. Once the collection has been amassed it can exist used for various criminal action or sold to interested parties on the dark web markets.
When the executable virus variants are concerned the victims can feel a wide variety of symptoms and consequences. One of the most mutual ones is the execution of a data harvesting component which can hijack both sensitive user information and create a consummate contour of the bachelor hardware. The collected data tin can exist used for crimes such every bit identity theft and financial corruption. Some of the most contempo attack campaigns also utilize the gained intelligence for bribery attacks. The hardware contour that is generated later this component has run tin event in the creation of an unique infection ID.
What's more dangerous is that the Rakuten virus tin can also exist used to manipulate various system settings and edit configuration files. This can allow for a persistent installation which is the automatic offset-upwards of the virus as soon as the figurer is powered on. Avant-garde viruses tin also block access to the recovery kick options which means that the victims will be unable to enter them. This can present a serious problem to the users as they will exist unable to follow most manual user removal instructions. In these situations we recommend that a professional anti-spyware solution is used.
If the virus infection includes any Windows Registry modifications so a wide variety of symptoms tin can exist identified. One of the about common ones is severe performance degradation to the pont of causing system instability. The virus can likewise cause the brandish of multiple errors and data loss.
The malware tin can also be used to deploy other threats to the infected hosts. A popular and circuitous malware delivery can be Trojan horses that are fabricated to establish a secure connection to a fix hacker-controlled server and allows for the hackers to spy on the victims in existent-fourth dimension, steal their data and take over control of their computers at any fourth dimension.
Another virus infection can exist the cryptocurrency miner — a dangerous script-based threat which will activate a download sequence. It will retrieve pocket-size-sized mathematical tasks that will have a heavy touch on on the system's performance: the CPU, retentiveness, hard disk drive space and etc. When one of them are reported every bit completed to the server the hackers will be rewarded with digital cryptocurrency directly to their wallets.
As the behavior can shift at whatsoever fourth dimension we recommend that victims of the Rakuten virus remove it at as soon as possible post-obit the initial infection.

Remove Rakuten Virus from Your Machine
In order to exist able to remove Rakuten virus, you should know where information technology's files and objects are hidden. The main idea is to follow the removal steps below. They are fabricated to help y'all isolate the virus and detect and delete the malicious files. For the complete detection and removal of Rakuten Virus, however, we strongly suggest that you lot download and run a costless scan with an advanced anti-malware software. Such tool volition automatically identify and eliminate all of the virus files and objects, related to any Rakuten Virus from your computer plus protect it in the future too.
- Guide 1: How to Remove Rakuten Virus from Windows.
- Guide 2: Go rid of Rakuten Virus on Mac OS X.
- Guide three: Remove Rakuten Virus in Google Chrome.
- Guide 4: Erase Rakuten Virus from Mozilla Firefox.
- Guide 5: Uninstall Rakuten Virus from Microsoft Edge.
- Guide 6: Remove Rakuten Virus from Safari.
- Guide 7: Eliminate Rakuten Virus from Internet Explorer.
- Guide eight: Disable Rakuten Virus Button Notifications in Your Browsers.
Windows Mac Bone X Google Chrome Mozilla Firefox Microsoft Edge Safari Internet Explorer Stop Button Pop-ups
How to Remove Rakuten Virus from Windows.
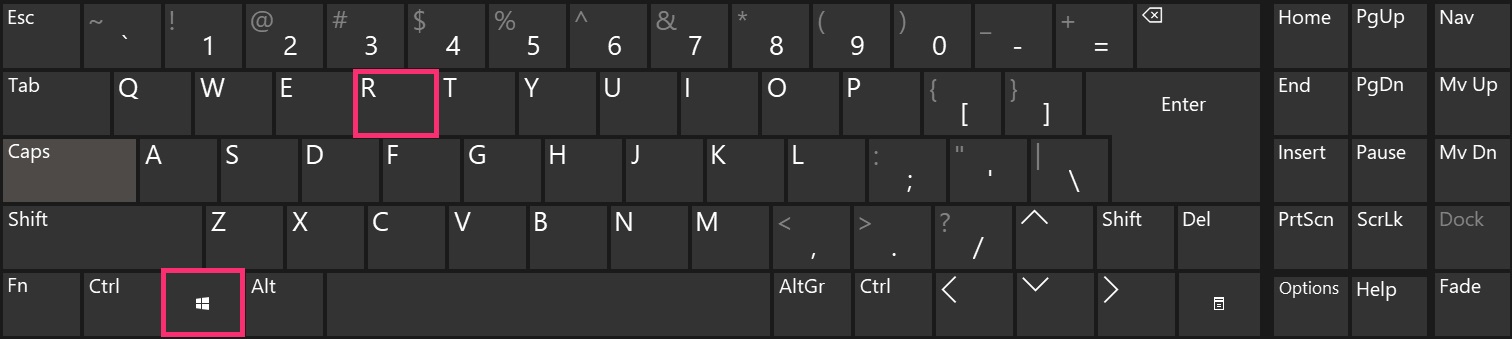
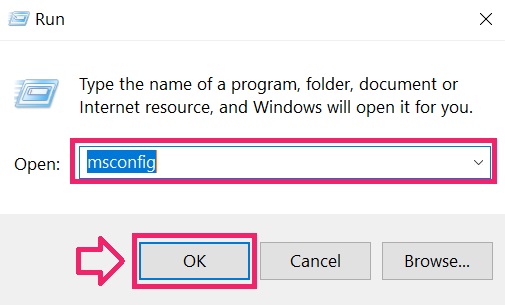
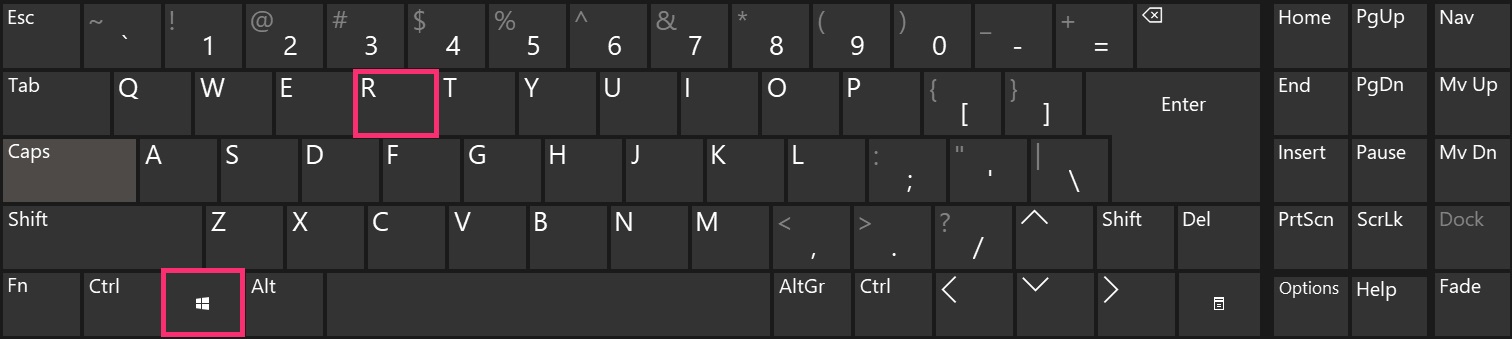
Pace one: Boot Your PC In Safe Mode to isolate and remove Rakuten Virus


Pace 2: Uninstall Rakuten Virus and related software from Windows
Here is a method in few easy steps that should be able to uninstall near programs. No affair if you are using Windows 10, 8, seven, Vista or XP, those steps will get the job washed. Dragging the programme or its folder to the recycle bin tin exist a very bad decision. If yous do that, $.25 and pieces of the program are left behind, and that can atomic number 82 to unstable work of your PC, errors with the file blazon associations and other unpleasant activities. The proper way to get a programme off your computer is to Uninstall it. To do that:

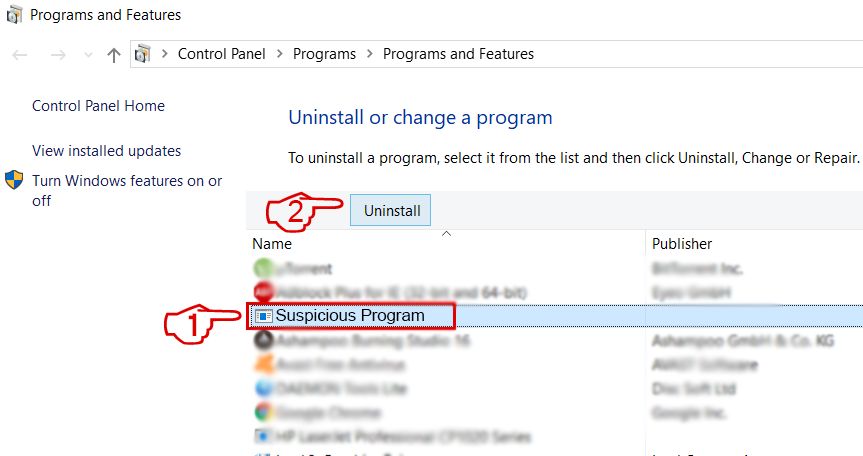 Follow the instructions higher up and you will successfully uninstall most programs.
Follow the instructions higher up and you will successfully uninstall most programs.
Footstep 3: Clean any registries, created past Rakuten Virus on your reckoner.
The usually targeted registries of Windows machines are the post-obit:
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
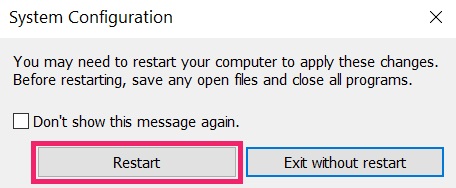
Y'all can access them by opening the Windows registry editor and deleting whatever values, created by Rakuten Virus in that location. This tin can happen by following the steps underneath:
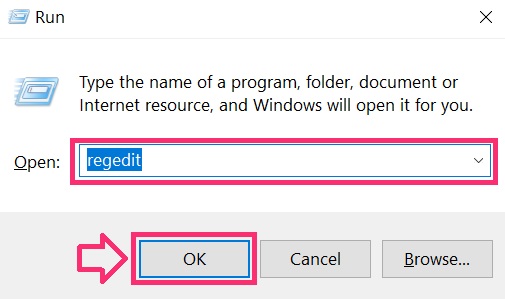
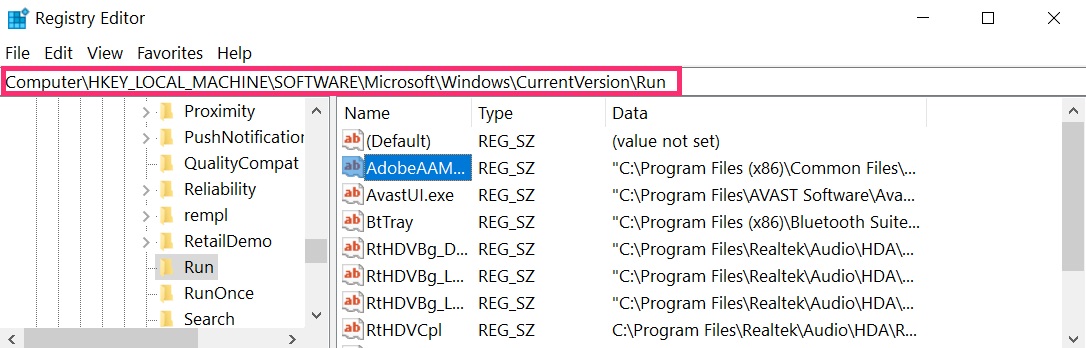
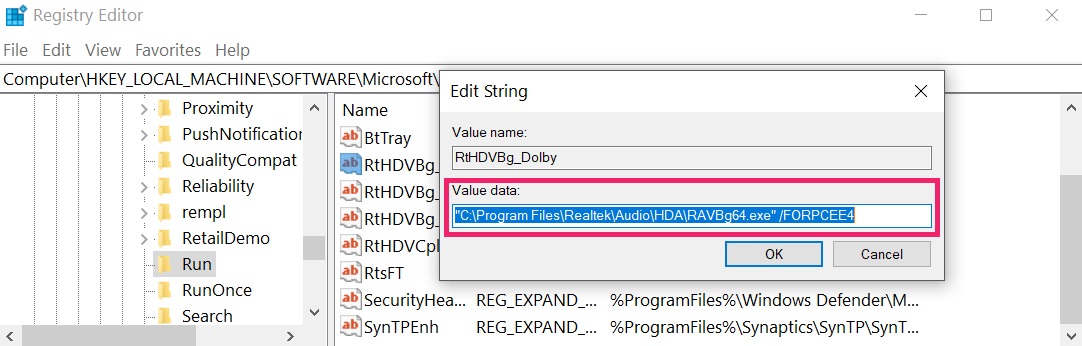 Tip: To find a virus-created value, yous tin can correct-click on it and click "Modify" to run into which file it is set to run. If this is the virus file location, remove the value.
Tip: To find a virus-created value, yous tin can correct-click on it and click "Modify" to run into which file it is set to run. If this is the virus file location, remove the value.
IMPORTANT!
Before starting "Pace 4", please boot back into Normal mode, in instance you are currently in Rubber Mode.
This will enable you to install and use SpyHunter v successfully.
Stride 4: Browse for Rakuten Virus with SpyHunter Anti-Malware Tool


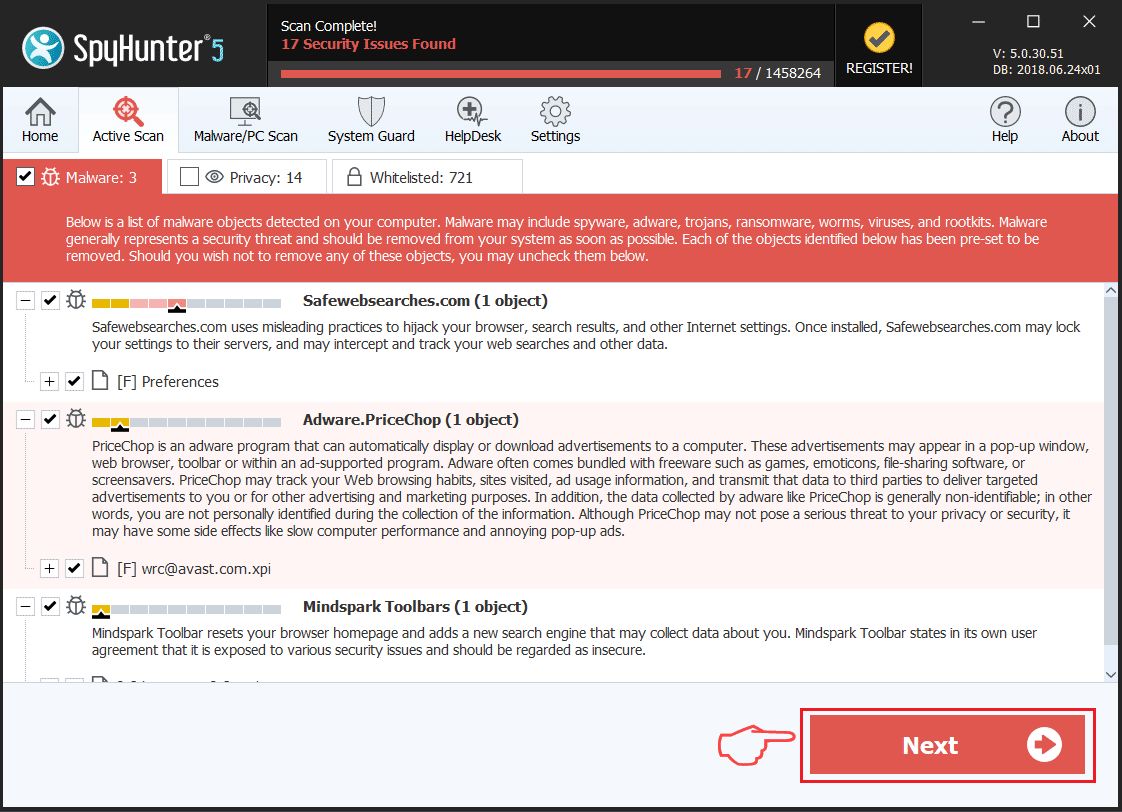
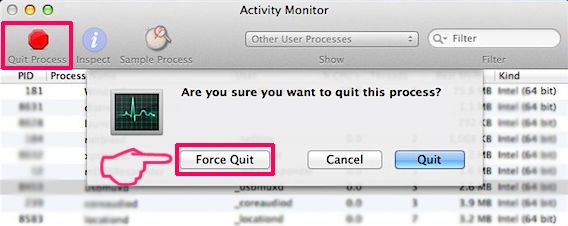
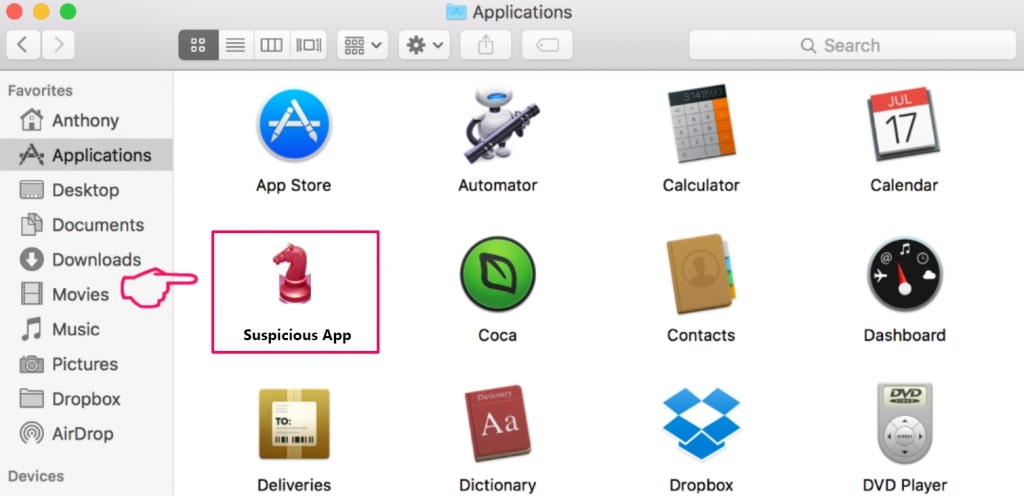
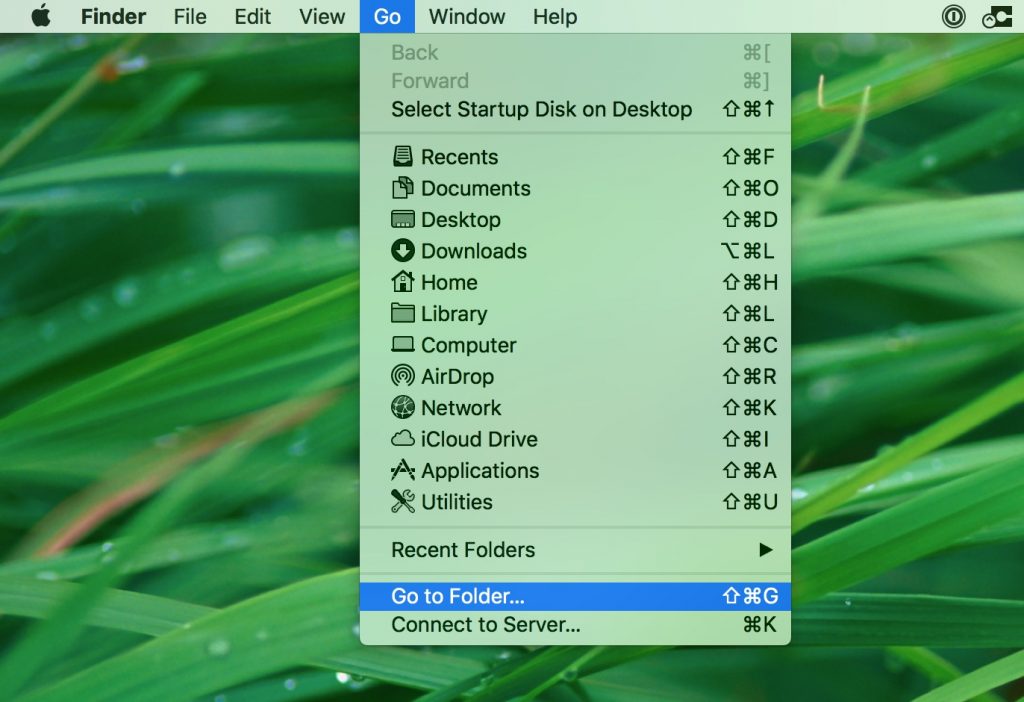
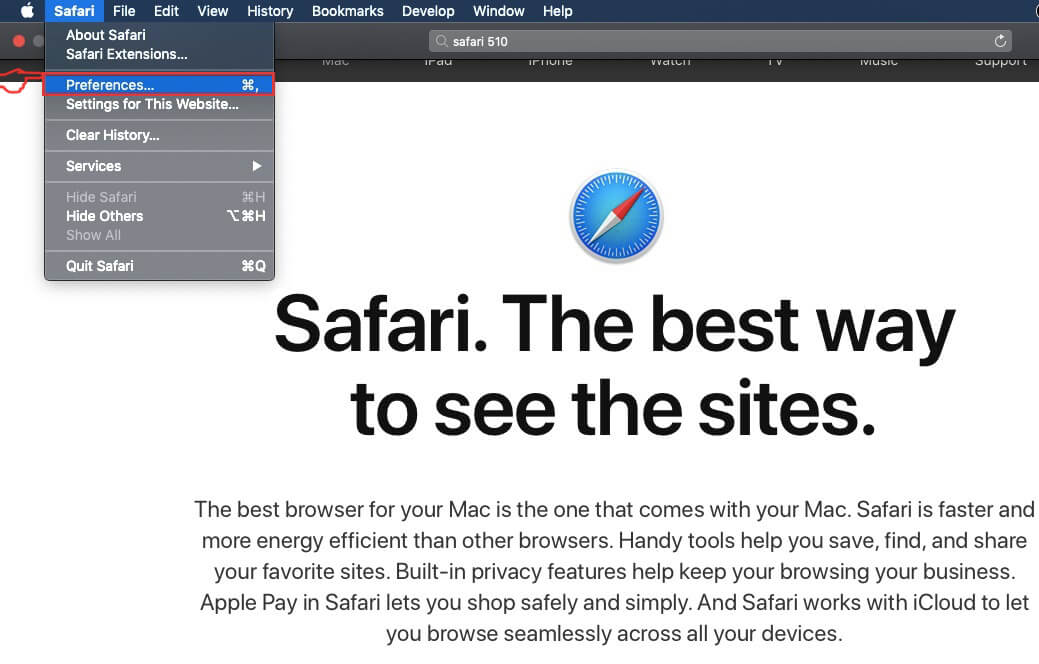
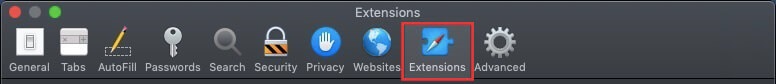
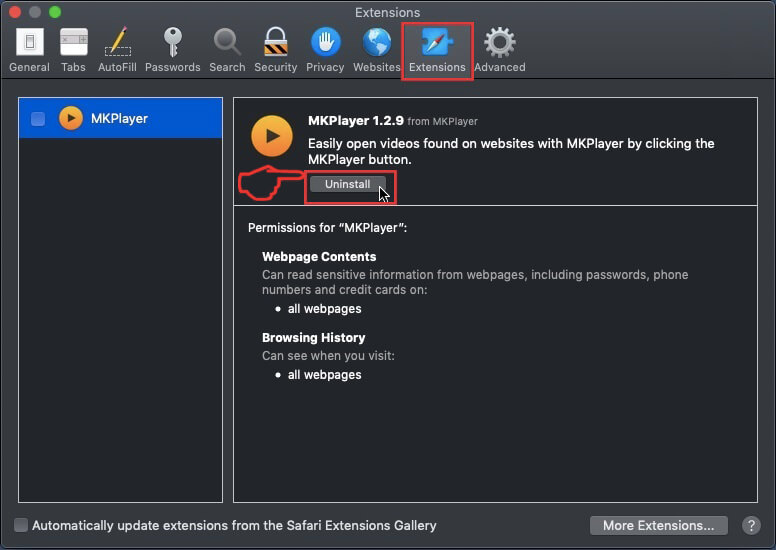
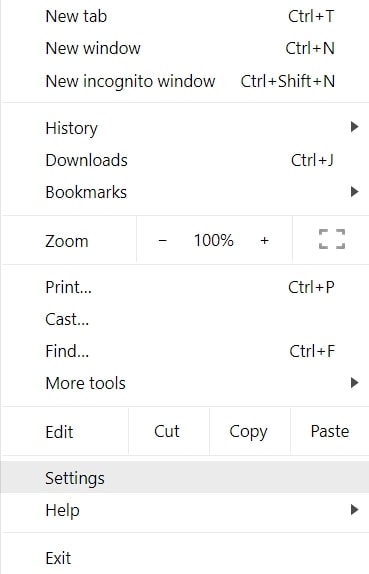
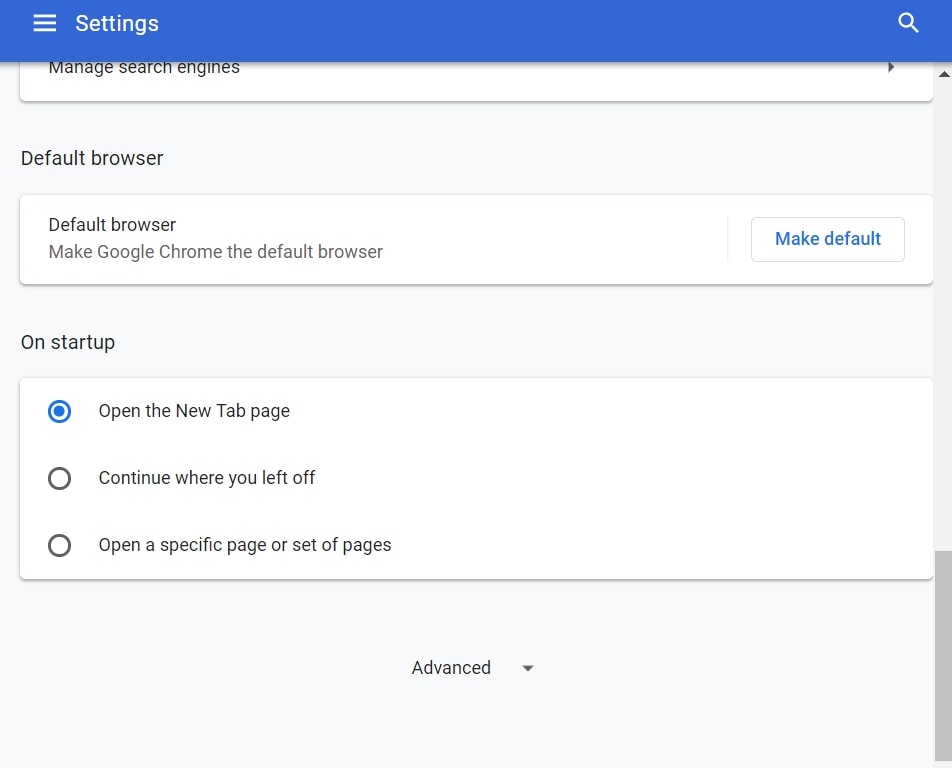
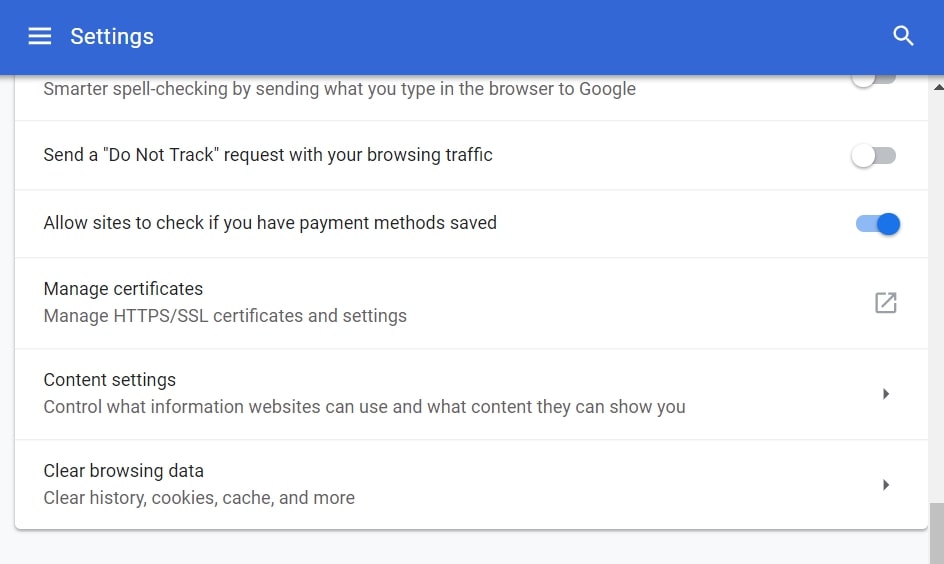
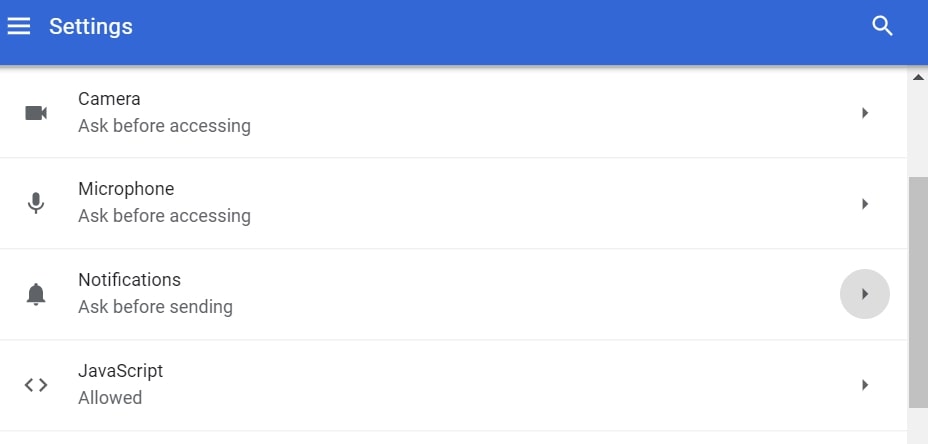
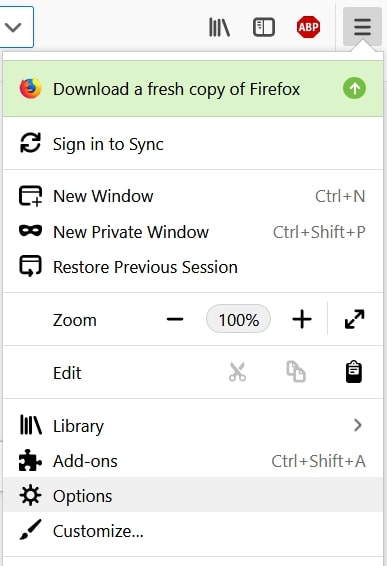
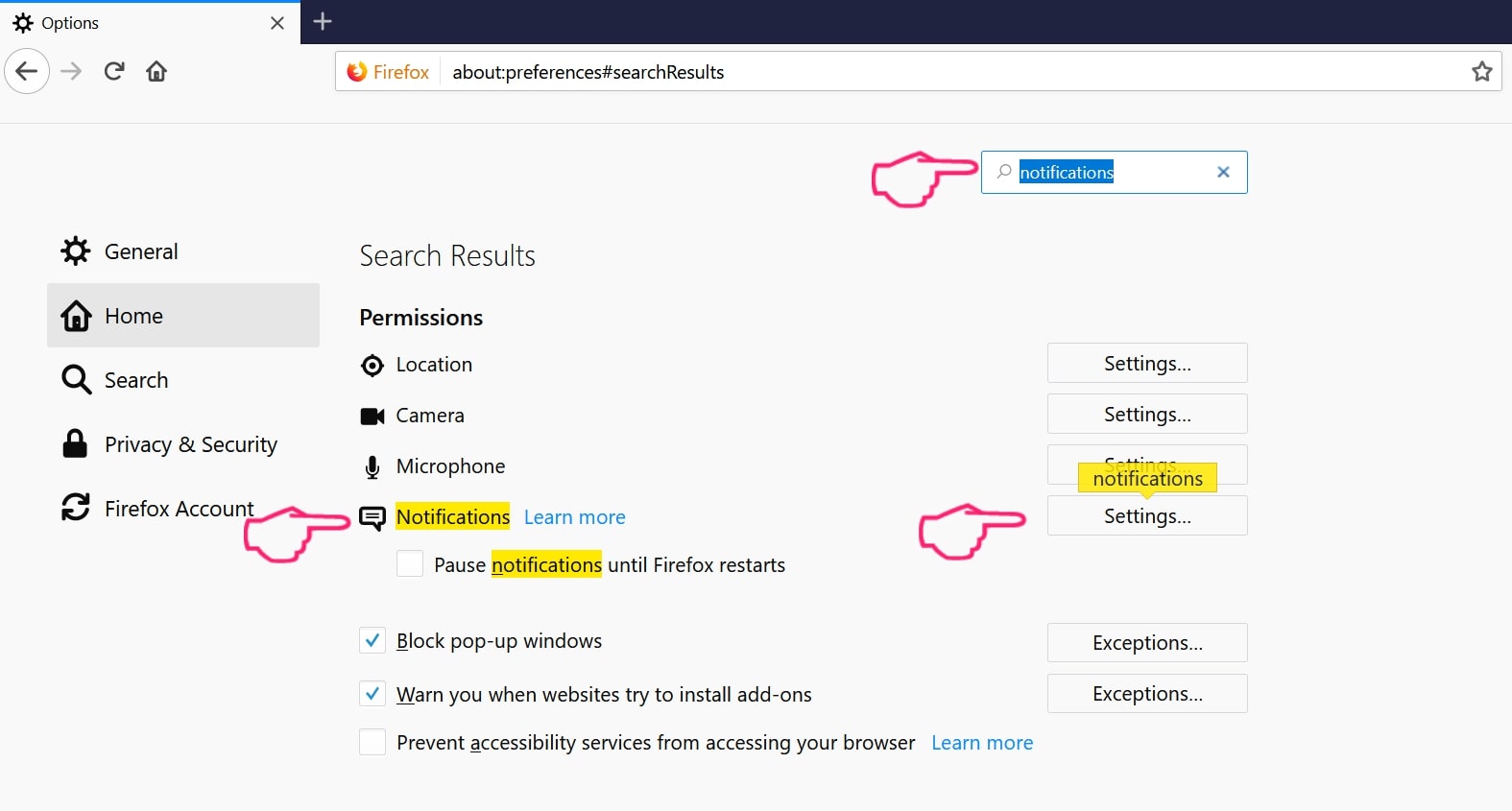
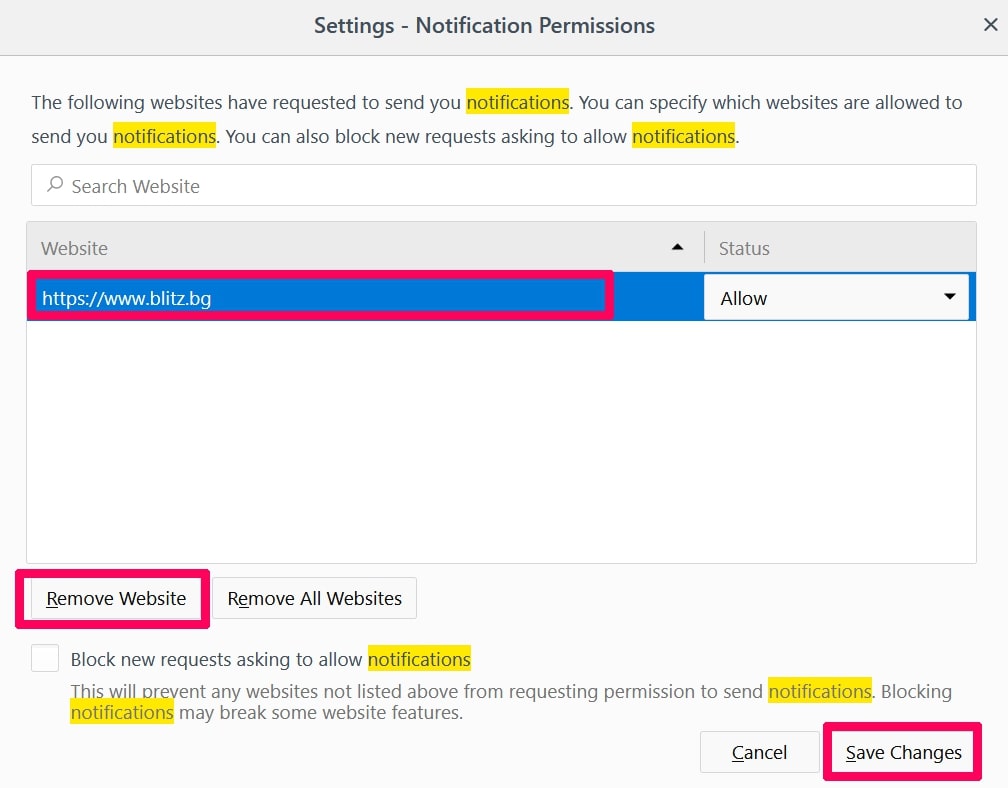
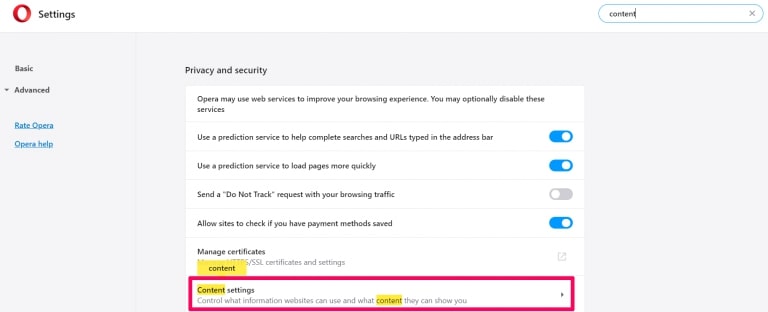
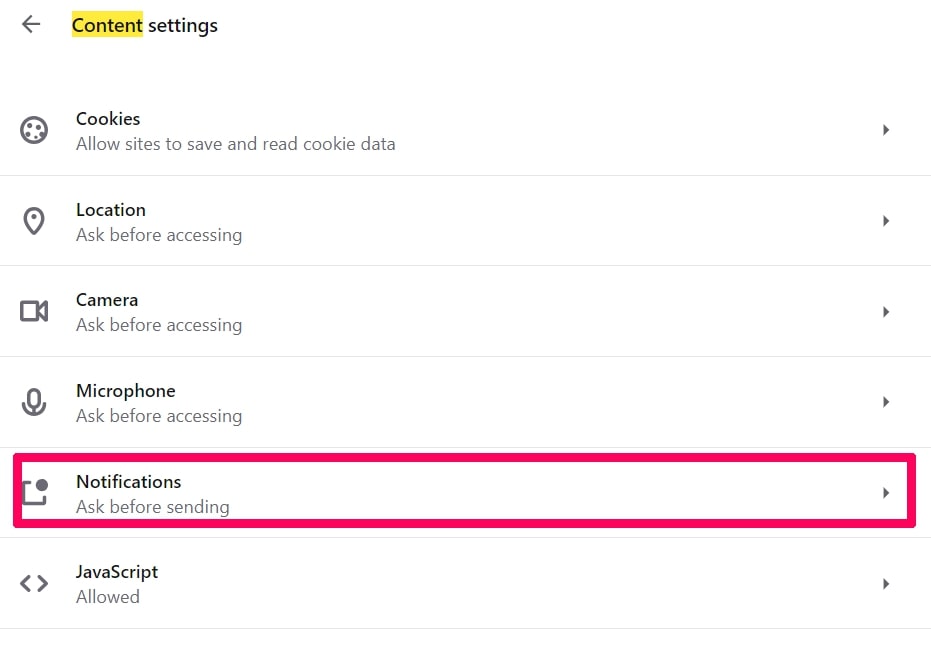
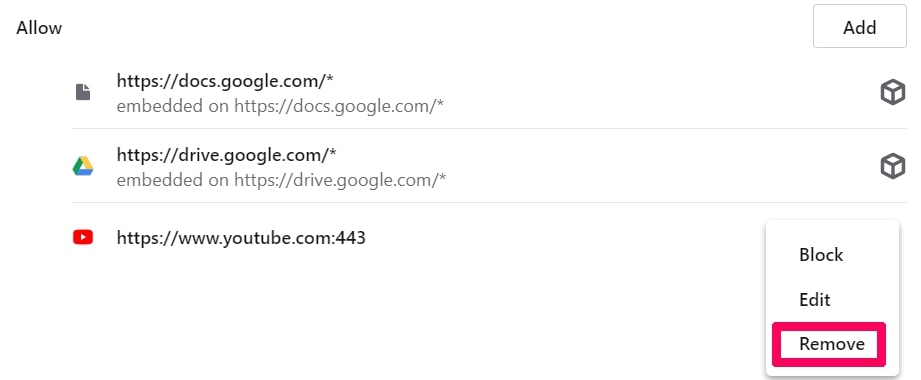
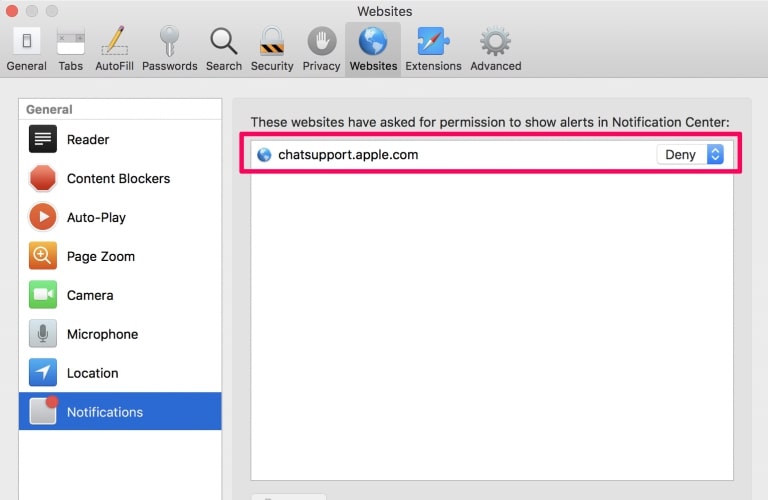
Step 1: Uninstall Rakuten Virus and remove related files and objects In case y'all cannot remove Rakuten Virus via Pace 1 above: In case you cannot find the virus files and objects in your Applications or other places we take shown above, y'all can manually look for them in the Libraries of your Mac. Only before doing this, please read the disclaimer beneath: Disclaimer! If you are about to tamper with Library files on Mac, be sure to know the name of the virus file, because if you delete the wrong file, it may cause irreversible damage to your MacOS. Continue on your own responsibility! You can echo the same procedure with the following other Library directories: → ~/Library/LaunchAgents Tip: ~ is there on purpose, considering information technology leads to more LaunchAgents. Pace ii: Scan for and remove Rakuten Virus files from your Mac When you are facing problems on your Mac every bit a consequence of unwanted scripts and programs such as Rakuten Virus, the recommended style of eliminating the threat is by using an anti-malware program. SpyHunter for Mac offers advanced security features along with other modules that volition amend your Mac'due south security and protect information technology in the time to come. Download SpyHunter for Mac Step i: Showtime Google Chrome and open the drop menu Stride ii: Move the cursor over "Tools" and then from the extended menu choose "Extensions" Step 3: From the opened "Extensions" card locate the unwanted extension and click on its "Remove" push button. Step 4: After the extension is removed, restart Google Chrome by closing it from the red "X" button at the meridian right corner and commencement it once more. Step one: Starting time Mozilla Firefox. Open up the menu window Step 2: Select the "Add-ons" icon from the carte. Step 3: Select the unwanted extension and click "Remove" Footstep 4: Afterwards the extension is removed, restart Mozilla Firefox by closing information technology from the red "X" button at the meridian correct corner and starting time it once more. Pace i: Start Edge browser. Step two: Open the drop card by clicking on the icon at the top right corner. Pace 3: From the drop menu select "Extensions". Pace iv: Choose the suspected malicious extension yous want to remove and and then click on the gear icon. Footstep five: Remove the malicious extension by scrolling down and then clicking on Uninstall. Pace i: Start the Safari app. Step ii: After hovering your mouse cursor to the acme of the screen, click on the Safari text to open up its drop down carte. Footstep 3: From the menu, click on "Preferences". Pace iv: After that, select the 'Extensions' Tab. Step 5: Click in one case on the extension yous want to remove. Step vi: Click 'Uninstall'. A pop-up window will appear asking for confirmation to uninstall the extension. Select 'Uninstall' again, and the Rakuten Virus will exist removed. Step 1: Start Internet Explorer. Footstep 2: Click on the gear icon labeled 'Tools' to open up the drop menu and select 'Manage Add-ons' Step three: In the 'Manage Add-ons' window. Stride 4: Select the extension you want to remove and then click 'Disable'. A pop-up window will announced to inform you that you are about to disable the selected extension, and some more add-ons might be disabled as well. Get out all the boxes checked, and click 'Disable'. Pace 5: After the unwanted extension has been removed, restart Internet Explorer by closing it from the red '10' button located at the acme right corner and start it again. Plow Off Push Notifications from Google Chrome To disable any Push Notices from Google Chrome browser, please follow the steps below: Step 1: Go to Settings in Chrome. Step 2: In Settings, select "Advanced Settings": Step iii: Click "Content Settings": Pace iv: Open up "Notifications": Step five: Click the three dots and choose Block, Edit or Remove options: Remove Button Notifications on Firefox Stride 1: Go to Firefox Options. Stride 2: Become to "Settings", type "notifications" in the search bar and click "Settings": Step 3: Click "Remove" on any site yous wish notifications gone and click "Save Changes" Stop Push Notifications on Opera Step 1: In Opera, press ALT+P to get to Settings Stride 2: In Setting search, type "Content" to go to Content Settings. Footstep 3: Open Notifications: Step four: Do the same every bit you did with Google Chrome (explained beneath): Eliminate Push button Notifications on Safari Step one: Open Safari Preferences. Stride 2: Cull the domain from where you like push pop-ups gone and change to "Deny" from "Let".
Windows Mac OS 10 Google Chrome Mozilla Firefox Microsoft Border Safari Net Explorer Stop Push button Popular-ups
Go rid of Rakuten Virus from Mac Bone X.
one. Hit the ⇧+⌘+U keys to open Utilities. Another way is to click on "Go" then click "Utilities", similar the image below shows: 


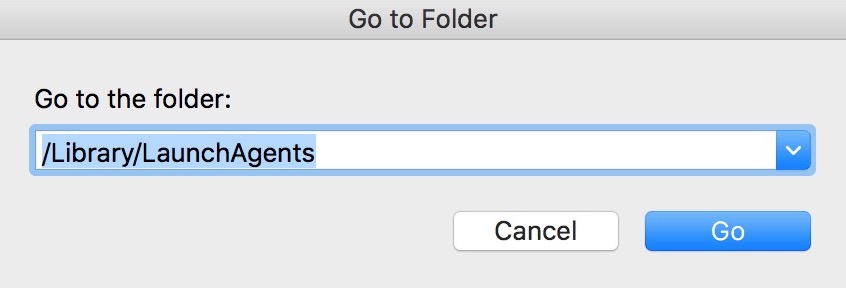
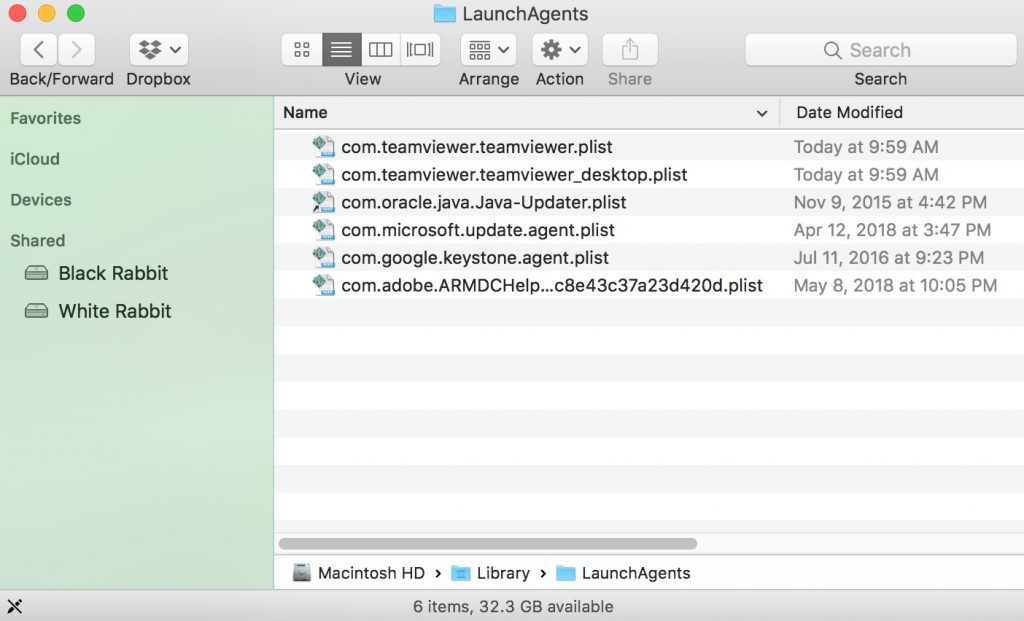
/Library/LaunchDaemons
Windows Mac OS X Google Chrome Mozilla Firefox Microsoft Edge Safari Internet Explorer Cease Push Pop-ups
Remove Rakuten Virus from Google Chrome.



Windows Mac Bone X Google Chrome Mozilla Firefox Microsoft Border Safari Internet Explorer Stop Push Pop-ups
Erase Rakuten Virus from Mozilla Firefox.



Windows Mac Os X Google Chrome Mozilla Firefox Microsoft Edge Safari Cyberspace Explorer End Push Popular-ups
Uninstall Rakuten Virus from Microsoft Border.




Windows Mac OS X Google Chrome Mozilla Firefox Microsoft Border Safari Internet Explorer Stop Button Pop-ups
Remove Rakuten Virus from Safari.
Windows Mac OS X Google Chrome Mozilla Firefox Microsoft Edge Safari Internet Explorer Stop Push Pop-ups
Eliminate Rakuten Virus from Internet Explorer.



Remove Push Notifications acquired by Rakuten Virus from Your Browsers.


Source: https://sensorstechforum.com/rakuten-virus-remove/


0 Response to "How To Remove Rakuten From Chrome"
Post a Comment